In this blog I detailed out the necessary security settings that we’re putting into place to protect your information in the cloud. The cloud doesn’t arrive secure, backed up, or tuned to your individual needs. Threats change constantly, regulatory and business needs change too. We care about your business so we work to stay on top of the latest threats and use the tools included in Office 365 to keep things secured. Nothing is 100% of course, but we try to keep you from being the low hanging fruit. Small business is the #1 favorite target for the bad guys.
It has always been the case that the hardest part of security was finding out in time that you have a problem. It used to be very expensive to monitor for security issues. Now we have the tools and so it’s time to use them. Part of what we’ve done is to set up alerts. These alerts are designed to inform you about changes that might threaten your data. We’ve set up several of them for you. More can be setup to monitor just about anything so if you have some ideas of what you’d like to know about we can probably set up an alert to keep you informed. We consider these just the bare minimum set. You may want more and that can be accommodated. These alerting tools are very powerful. So if you have a concern we can probably set an alert for it.
We’ve gotten a few questions about what the alerts mean. I’m going to show you a sample of each alert that you can expect and interpret what it is saying and what it means for you.
Alert a File has been deleted
We have set an alert to let you know when a file has been deleted. In the course of a day it is normal for files to be deleted however, if a single person deletes a whole bunch of files then you might have a problem. We have seen cases where existing employees “clean-up” files before they leave. We’ve also seen cases where infections delete files. We’ve seen cases where an employee moves files from one place to another accidentally. These alerts will let you become aware of these situations.
How to read this alert: Highlighted in yellow is the type of alert. A file has been deleted. Looking at the user (red arrow) I see that it was Ted. Looking at the item deleted (red underline) I see that it’s a PDF file. I know that this is normal activity from Ted. And because I didn’t get a flurry of these I’m not worried about it. However, if I was I can get right into researching the problem buy clicking on any of the links in the What’s Next section (red circled). Office 365 documents what happens to every file and every user activity. I will say that if searching logs isn’t a normal activity for you it won’t be very intuitive but we’re ready to help with that. We just need you to help identify what is a problem and what is normal activity. This is why the alerts are important. 
Alert Someone has shared data
We have set an alert to let you know when your data has been shared outside of your company. We have seen cases where employees have shared sensitive information with competitors sometimes maliciously. We have seen employees share data to their personal accounts. When you boil down what your company really owns it is your information. This alert will let you know when your property is being shared with someone outside of your business. Sometimes it’s fine and expected. Sometimes it is not. This alert will allow you to make an informed decision and be aware of who has your data.
How to read this alert: Highlighted in Yellow is the type of alert. This one tells us that someone shared data. Looking at the user (red arrow) I see that it was Amy (me). Looking at the item I see that it is a OneNote document (red underline) and under that blacked out bit I see the file name. In this case I was sharing our documentation with a developer for a project that he is working on with our client. This is normal and expect activity so I can just delete the alert. But if I was concerned about it we could stop this share and prevent access to the file. We could also use the links in the red circled area to check to see if there’s been any other such activity that we might need to put an end to.
Alert Password Changes
We have setup an alert to let you know when someone changes their password. On the surface of that it doesn’t sound like a big deal but it really is. Because that someone might not be you. This alert will go to the person whose password changed. If they just changed their password then there’s nothing to do. But if they didn’t then this alert will let us know that there’s been a successful hack. Passwords are the most vulnerable part of every network. In the case of an account with administrator access, everyone with administrator access will get a notification. We’ve set that alert extra high because of the powerful nature of those permission levels.
How to read this alert: Highlighted in Yellow is the type of alert. This one tells us that a password has changed. We can see whose password changed in the user section (red arrow). Under that blacked out bit is the email address of the account that has the new password. The time of the activity can also be important for this alert. So note when this occurred (red underline). If it is a hack situation often the time will be in the middle of the night or early morning. They hope to go unnoticed. If you’d like more information about this alert you can click in the What’s Next section (red circle). If there was a suspicion our first action would be to reset the password. Then look at the logs to determine where the problem came from.
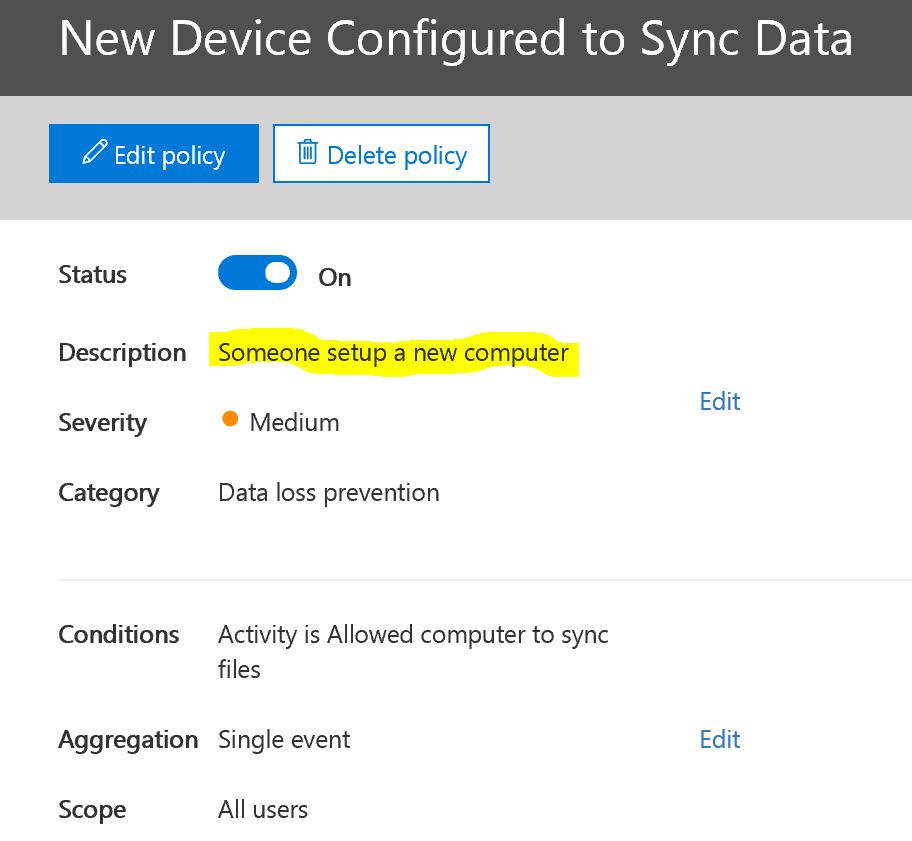
Alert a new device is syncing data
You will receive an alert when a new computer/phone/tablet, what we refer to generically as a device, starts syncing your data down onto itself. You would expect this to occur if it is a computer owned by your company but if it isn’t then there’s likely a problem. This alert will tell us where your data went to.
Fortunately I don’t have an alert to show you for this one. But you’ve seen the format above and this one will look the same. Below are the settings. You will only get this message when a new computer is setup and for no other reason. So it should occur very rarely. If this alert occurs you will want to note the name of the computer. If you don’t recognize it, then we need to investigate.
As I mentioned at the top, these alerts are a baseline. We have the tools to do more. I hope that these will give you some ideas of what else you might like to know about should it occur. We’ve got the tools now to allow you to keep on top of things and stay aware of where your data is going and who now owns it. With data if you possess it, you own it. We’ve seen bad things happen as a result so we’re very happy to have these tools available to help keep you safe.
– Amy, president
About Harbor Computer Services
Harbor Computer Services is an IT firm servicing Southeastern Michigan. We work exclusively under contract with our clients to provide technology direction and either become the IT department or provide assistance to the internal IT they already have. We have won many awards for our work over the years, including the worldwide Microsoft Partner of the Year in 2010. We’re the smallest firm to have ever won this most prestigious award. Most recently we were recognized as one of the top 20 visionaries in small business IT by ChannelPro Magazine (2015). And in 2016 as the top Michigan IT firm for Manufacturing. There are a few simple things that make Harbor Computer Services the best choice for your business. •We are Professionals •We are Responsible •We are Concerned About The Success of Your Business