This morning on twitter there is a thread about the hacking of an individual who considers himself low profile on the internet. The short video, 5 minutes, is worth your time. In this video, the ethical hacker (which is someone who is known to the victim and hacks for the purpose of education) is announcing that she is going to hack this individual. During that announcement, the hack happens.
You’re never going to be more alert for a potential hack then when you sign up to be hacked and you’re recording a video about it. Yet it happens so easily. Scroll down below the video to understand how this happened and how you can avoid being the next victim.
In this case, the phone call was spoofed. It was also very short. There’s a lot of background noise and the caller simple says, check email! The victim checks his email, he’s expecting a very important email and so doesn’t pay much attention to the spoofed address that it came from. He opens the email, opens the attachment and the hack is done. What does the victim see? He sees a normal looking document. Nothing bad happens to his computer. He has no idea that anything bad happen. What actually happened is that he provided the hackers with remote access to his computer and then they were able to see anything he opened or logged into.
Hacks are quiet.
Avoid being the next victim
From the hacker herself.
“Mitigations for this hack include: 1. Keep machines patched (a patch exists for this vuln but his machine was out of date) 2. Delist from data brokerage sites (w/ a tool or manually) 3. Use 2 methods of communication to verify before taking requested action from an urgent email”
What does this mean for you?
- Never turn down the opportunity to patch your computer, or apply updates right now. If his MAC was updated, this hack would not have worked.
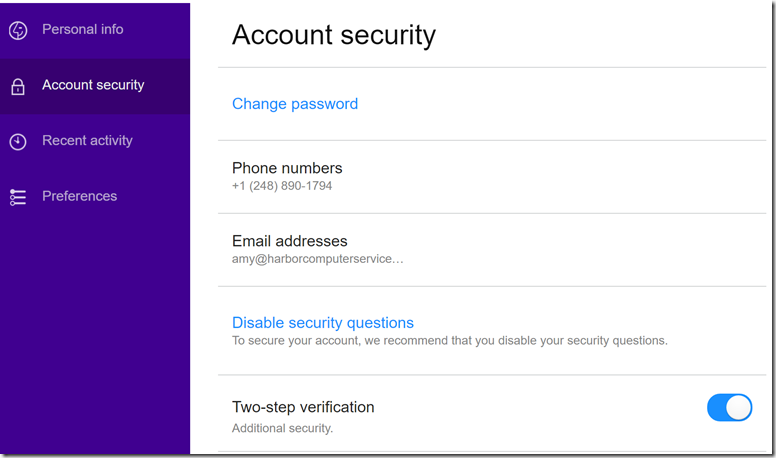
- Pay attention to the Darkweb ID reports that we send out. Go to those accounts, change the password and never use the same password twice. A password tool, like Roboform, works wonders for this. We can help you get setup.
- Never immediately respond to an email or a text. Don’t reply to that email. Use another previously tested way to reach that person to verify first. If you receive an email, call or text that person using a phone number that you already know to be legitimate, not the one in the potentially spoofed email. Do not click until you verify.
- Every employee is a potential entry point into your business. Don’t leave anyone out of security training and password tools.
Social engineering is the most powerful weapon of the hacker. They use psychology against you. It’s hard not to fall for it. Anyone can. This is why you need tools like password tools, education, updating and processes for verification before clicking.
Harbor Computer Services is an IT firm servicing Southeastern Michigan. We work exclusively under contract with our clients to provide technology direction and either become the IT department or provide assistance to the internal IT they already have. We win awards! Recently we were recognized in the gratitude category for our corporate culture by dBusiness magazine.
There are a few simple things that make Harbor Computer Services the best choice for your business. •We are Professionals •We are Responsible •We care about your business