We have two important changes to announce today. Often our work goes unnoticed as a lot of it happens in the background without a direct impact on how people go about their daily work life. Today we’re beginning deployment of a change will will necessarily impact procedures in the name of security.
If you’d like your staff to have a 15 minute tutorial on this new procedure, let us know. We’re happen to schedule an online meeting that they can attend for a first hand demo and opportunity to ask questions.
Email Quarantine Release Procedural Change
One of the threats that was pointed out in our recent security webinar is that the people that work in your business are your first line of defense. On our end we can configure settings, apply filters, and do all of the right things, but because we’re fighting against organized crime and nation-state espionage actors, we need every employee of yours to be educated and in this fight too.
To assist with this, we are planning to change the procedure for releasing a captured email from quarantine, from one where your employees can release the suspect email, to one where they will request that an email be released. This will provide the opportunity for your tech to be a second set of eyes on that email before it gets released. Your staff isn’t infallible and could be fooled by a well-spoofed email. Harbor’s staff isn’t infallible either. But with a second set of eyes upon the questionable email, we can hopefully avoid a costly mistake. If Harbor’s staff has a serious concern about the email we do have tools which they may use to open and “detonate” the content and links in that email into a sand-boxed safe environment before releasing the email into your inbox. This won’t happen for every email, just those that they have a very serious question about.
Here is what the new process looks like from your point of view. Below is an image from the quarantine report that gets delivered to you daily.
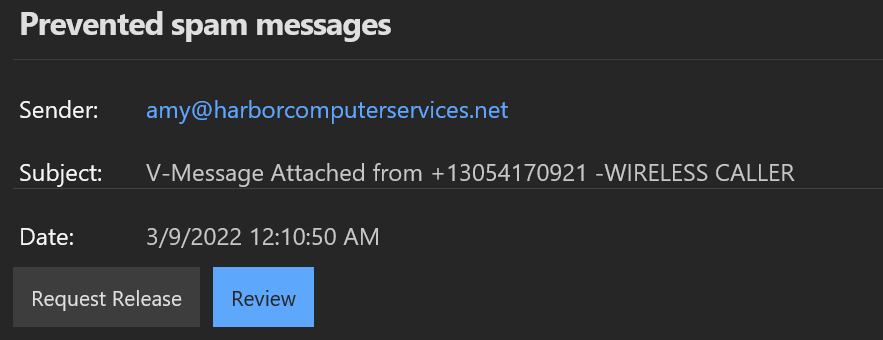
The Review button should be used first. It will open a picture of the email and allow the recipient to look at the content and make a determination of whether they need it sent to their Inbox or not. If after you have reviewed the email and you would like it sent to your Inbox, then press the Request Release button.
The Request Release button will send a message to the harbor@yourcompany.com email address which goes into a channel dedicated to you in our alerts team. Your tech will then review the item that has been requested for release and make the determination of whether they should release, reject or detonate the content of the email. You will get a message back letting you know what the determination was.
This process will take some time, however, we do expect to be able to fulfill the request the same day that you send it. I realize that this causes a delay but for the sake of security its a necessary one. If you have questions about this process, please reach out.
Please share this new process with all of your employees who receive email.
What about false captures? Or emails that we’re captured but should have been?
If you frequently get messages caught in quarantine that shouldn’t be, then we need your help to train the system to better meet your needs. Similarly, if messages are coming into your Inbox that are phishing emails or otherwise pose a danger, then we also need your help to train the system to do better.
Here’s how you can help
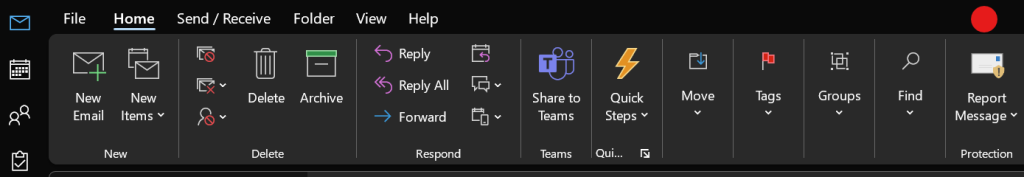
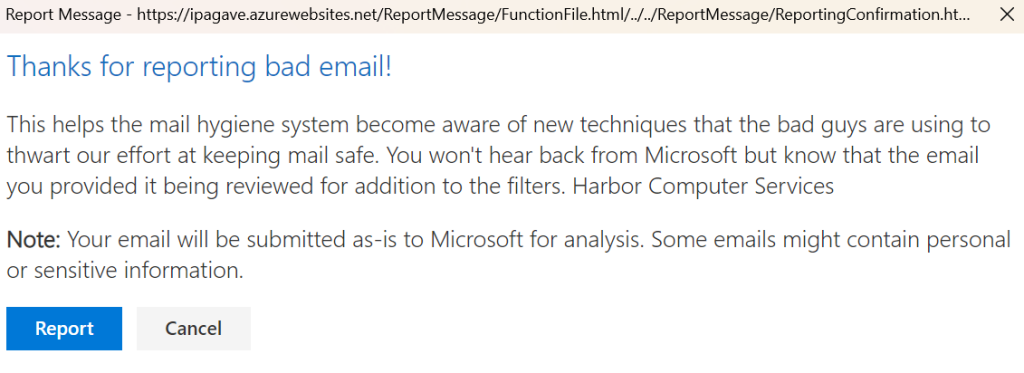
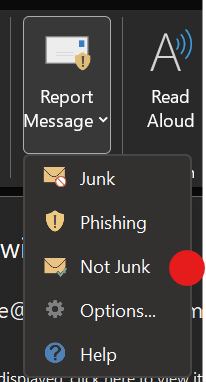
When a dangerous message gets delivered to your Inbox. In Outlook, when you are viewing a message, in your toolbar there is item called Report Message. Click on that and choose Phishing email. This will fire off the Report Email tool. Click Report and the message will be removed from your Inbox, reported to Microsoft as something that they need to analyze and block and it will also alert us that a bad message has made it through.
When a good message gets delivered to your Junk Mail folder. The process is similar. You will use the Report Email tool only this time you will select Not Junk. When you select this option the email will be moved to your Inbox and a report will be generated to aid in it not happening again.
Groups Automation
The second thing that I wanted to tell you about today, is a reconfiguring of how security groups are created and managed. This is the first step in the process of implementing the new Endpoint Manager and Defender for Business features of your subscription that were announced earlier.
We are making a change that will convert security groups to what are called Dynamic Groups. Dynamic Groups are able to add and remove members based upon the characteristics of that person or device, thus eliminating situations where people are manually added and perhaps forgotten later. Instead, while the person or device has the defined characteristic they are a member of that security group and when they no longer have that characteristic they are automatically removed from that group.
In the long run this will reduce administrative overhead and provide greater security by reducing the potential for error. There is no visible change or process change that you’ll see from this. Its fully a back end configuration.
Harbor Computer Services is an IT firm servicing Southeastern Michigan. We work exclusively under contract with our clients to provide technology direction and either become the IT department or provide assistance to the internal IT they already have. We win awards! Recently we were recognized in the gratitude category for our corporate culture by dBusiness magazine.
There are a few simple things that make Harbor Computer Services the best choice for your business. •We are Professionals •We are Responsible •We care about your business





One thought on “Email Quarantine policy change and Groups automation underway”